Streamline your technical communication process with an enterprise-class DITA CCMS.
MadCap IXIA CCMS
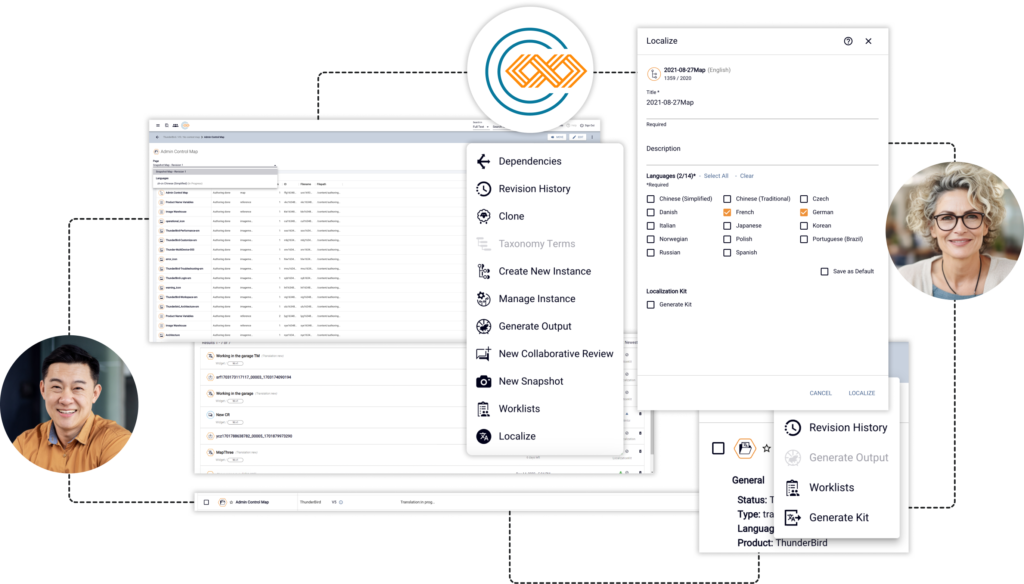
Author, collaborate, review, localize, deliver, and manage your DITA-based technical content with IXIA CCMS, anytime on any device.
Documentation
Access our product documentation.
Customer Support
Contact our support team to get the answers you need.
Choose a better way to publish content